

| Home | Log In | Register | Our Services | My Account | Contact | Help |
You are NOT currently logged in
Register now or login to post to this thread.
THE TALK TO YOURSELF THREAD. (NOWT)
goldfinger

 - 09 Jun 2005 12:25
- 09 Jun 2005 12:25
Thought Id start this one going because its rather dead on this board at the moment and I suppose all my usual muckers are either at the Stella tennis event watching Dim Tim (lose again) or at Henly Regatta eating cucumber sandwiches (they wish,...NOT).
Anyway please feel free to just talk to yourself blast away and let it go on any company or subject you wish. Just wish Id thought of this one before.
cheers GF.
Anyway please feel free to just talk to yourself blast away and let it go on any company or subject you wish. Just wish Id thought of this one before.
cheers GF.
VICTIM - 19 May 2017 14:56 - 76921 of 81564
Too many takeaways .
Fred1new

 - 19 May 2017 15:00
- 76922 of 81564
- 19 May 2017 15:00
- 76922 of 81564
Execc,
Perhaps the car got the wrong reporter.
Known as taking his legs from under him.
=-=-==-=
Have a sniff around the torrid parties so-called manifesto.
I think Fallon is a pompous blusterer defending the indefensible.
But do your own homework using your own Bible.
Perhaps the car got the wrong reporter.
Known as taking his legs from under him.
=-=-==-=
Have a sniff around the torrid parties so-called manifesto.
I think Fallon is a pompous blusterer defending the indefensible.
But do your own homework using your own Bible.
Fred1new

 - 19 May 2017 19:07
- 76923 of 81564
- 19 May 2017 19:07
- 76923 of 81564
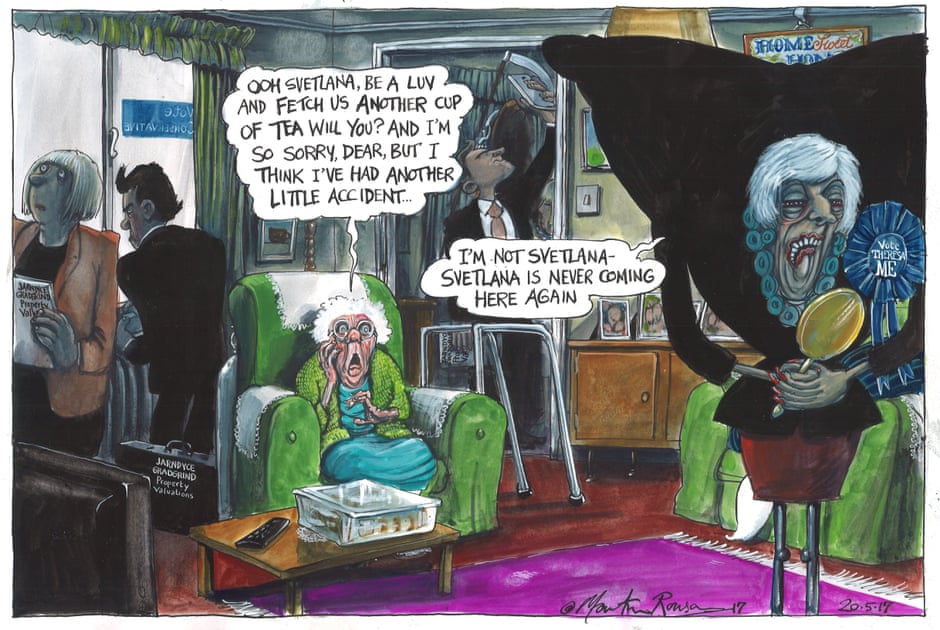
Theresa, another U-turn.
Not thought out policy.
Like Brexit and her ideas of a "deal".
May her God go with her.
Not thought out policy.
Like Brexit and her ideas of a "deal".
May her God go with her.
Fred1new

 - 20 May 2017 08:30
- 76924 of 81564
- 20 May 2017 08:30
- 76924 of 81564
aldwickkk - 20 May 2017 10:58 - 76925 of 81564
What the hell are they bothering to have a free vote on fox hunting , what a wast of parliamentary time when there are other urgent work to be done.
aldwickkk - 20 May 2017 11:01 - 76926 of 81564
.
aldwickkk - 20 May 2017 11:02 - 76927 of 81564
Fred1new Send an email to Fred1new View Fred1new's profile - 19 May 2017 19:07 - 76923 of 76925
Theresa, another U-turn.
Labour U-turn on Trident.
The Lady is not for turning
Theresa, another U-turn.
Labour U-turn on Trident.
The Lady is not for turning
VICTIM - 20 May 2017 11:26 - 76928 of 81564
Jeez I thought i was on , Freda moans relentlessly.com for a minute , phew .
ExecLine


 - 20 May 2017 18:23
- 76929 of 81564
- 20 May 2017 18:23
- 76929 of 81564
A bit of help for the NHS (or any other businesses or whatever still on Windows XP) in dealing with WannaCry infections and 'Ransomware lockups':
A group of security researchers have created a tool that can help users hit by the massive WannaCry ransomware attack decrypt their files without paying the ransom or wiping their device.
The tool, named Wanakiwi, is capable of defeating the WannaCry ransomware, which encrypts a user’s files and demands a payment made in Bitcoin in order for the victim to regain access to their machine.
WannaCry hit more than 300,000 machines in 150 countries last Friday, including computer systems of hospitals in England and major corporations around the world.
The Wanakiwi tool doesn’t work for all machines, but it has been tested and shown to be successful on Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008, Windows Server 2008 R2 and Windows 7 operating systems.
More at: Get a Wankawiwi for your Wannacry problem
A group of security researchers have created a tool that can help users hit by the massive WannaCry ransomware attack decrypt their files without paying the ransom or wiping their device.
The tool, named Wanakiwi, is capable of defeating the WannaCry ransomware, which encrypts a user’s files and demands a payment made in Bitcoin in order for the victim to regain access to their machine.
WannaCry hit more than 300,000 machines in 150 countries last Friday, including computer systems of hospitals in England and major corporations around the world.
The Wanakiwi tool doesn’t work for all machines, but it has been tested and shown to be successful on Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008, Windows Server 2008 R2 and Windows 7 operating systems.
More at: Get a Wankawiwi for your Wannacry problem
ExecLine


 - 20 May 2017 18:29
- 76930 of 81564
- 20 May 2017 18:29
- 76930 of 81564
Here's how it's done:
How To Decrypt Files From WannaCry
First, download the tool from GitHub at:
https://github.com/gentilkiwi/wanakiwi
—ideally on a machine that is free infection.
Extract the .zip file to a folder on your desktop. If you downloaded it on a machine other than the one hit by WannaCry, move the file to a USB drive and run it on the infected computer from the drive.
Open the tool by double clicking on it. Wanakiwi will begin searching the machine for the process tied to WannaCry. If they are named wnry.exe or wcry.exe, the tool should find them automatically.
If the tool can’t find WannaCry, it may be possible to manually identify the offending process by opening the Task Manager. This can be done by pressing Control + Alt + Delete on the keyboard. If there is a file that appears related to WannaCry, get the Process Identification Number (PID) and plug it into the command prompt after “wanakiwi.exe” to direct the tool to the ransomware.
Once the tool knows what it is targeting, it will begin searching for the decryption key. It does this by searching the system’s memory for prime numbers and piecing together the key used by the ransomware. The rest should be automatic; once Wanakiwi has the encrpytion key, it will decrypt the ransomed files on its own.
Once it is finished, users are advised to run an antivirus tool to remove any artifacts of WannaCry that may still be present on their system. To be safe, users may want to create backups of their most important files, wipe the machine and perform a fresh install of their operating system.
Wanakiwi doesn’t work 100 percent of the time—much of its success is dependent on timing, as it relies on reading the memory of the system at the time of the infection.
If the system is restarted or too many processes have been run since the infection, the encryption key might be lost or overwritten by data from other applications. But the tool does provide some hope for those who may still be plagued by ransomware.
How To Decrypt Files From WannaCry
First, download the tool from GitHub at:
https://github.com/gentilkiwi/wanakiwi
—ideally on a machine that is free infection.
Extract the .zip file to a folder on your desktop. If you downloaded it on a machine other than the one hit by WannaCry, move the file to a USB drive and run it on the infected computer from the drive.
Open the tool by double clicking on it. Wanakiwi will begin searching the machine for the process tied to WannaCry. If they are named wnry.exe or wcry.exe, the tool should find them automatically.
If the tool can’t find WannaCry, it may be possible to manually identify the offending process by opening the Task Manager. This can be done by pressing Control + Alt + Delete on the keyboard. If there is a file that appears related to WannaCry, get the Process Identification Number (PID) and plug it into the command prompt after “wanakiwi.exe” to direct the tool to the ransomware.
Once the tool knows what it is targeting, it will begin searching for the decryption key. It does this by searching the system’s memory for prime numbers and piecing together the key used by the ransomware. The rest should be automatic; once Wanakiwi has the encrpytion key, it will decrypt the ransomed files on its own.
Once it is finished, users are advised to run an antivirus tool to remove any artifacts of WannaCry that may still be present on their system. To be safe, users may want to create backups of their most important files, wipe the machine and perform a fresh install of their operating system.
Wanakiwi doesn’t work 100 percent of the time—much of its success is dependent on timing, as it relies on reading the memory of the system at the time of the infection.
If the system is restarted or too many processes have been run since the infection, the encryption key might be lost or overwritten by data from other applications. But the tool does provide some hope for those who may still be plagued by ransomware.
Chris Carson

 - 20 May 2017 19:07
- 76931 of 81564
- 20 May 2017 19:07
- 76931 of 81564
Wankawiwi? sounds like an Ann Summers free gift :0)
ExecLine


 - 21 May 2017 00:12
- 76932 of 81564
- 21 May 2017 00:12
- 76932 of 81564
Knock out a bad Review and you could get sued for Libel and also Financial Damages:
https://inews.co.uk/opinion/woman-faced-legal-action-bad-review-tripadvisor-worried/
https://inews.co.uk/opinion/woman-faced-legal-action-bad-review-tripadvisor-worried/
Fred1new

 - 21 May 2017 09:34
- 76933 of 81564
- 21 May 2017 09:34
- 76933 of 81564

aldwickkk - 21 May 2017 14:51 - 76934 of 81564
The Work and Pensions Secretary explained how social care would be funded by the Conservatives.
Damian Green said using the estate to pay for it and then inheriting £100,000 was "reasonable".
Didn't see what he said about it. So if you needed social care for say two months before you died, they would sell your house worth say £300,000 and give you £100,000., or could you pay the social care bill for the two months and keep the house ?
Damian Green said using the estate to pay for it and then inheriting £100,000 was "reasonable".
Didn't see what he said about it. So if you needed social care for say two months before you died, they would sell your house worth say £300,000 and give you £100,000., or could you pay the social care bill for the two months and keep the house ?
aldwickkk - 21 May 2017 15:15 - 76935 of 81564
Execline
“The material you have posted about our client on Tripadvisor.com is defamatory and therefore unlawful,” Not if it's true ?
“The material you have posted about our client on Tripadvisor.com is defamatory and therefore unlawful,” Not if it's true ?
ExecLine


 - 21 May 2017 15:40
- 76936 of 81564
- 21 May 2017 15:40
- 76936 of 81564
alders
I do agree with you. A comment cannot really be defamatory if it's true.
But a letter from a lawyer only costs a "£100 x 'a few'" and can often work miracles or get good results.
In this case, the threatened lady asked TripAdvisor if her comment could be taken down.
If this was done, the lawyer's client restaurateur got the desired result - and also deterred others from making similar unfavourable comments.
IMHO, the best way to deal with bad restaurant service, is to 'use your boots to do the talking and walk away, never to return'.
I do agree with you. A comment cannot really be defamatory if it's true.
But a letter from a lawyer only costs a "£100 x 'a few'" and can often work miracles or get good results.
In this case, the threatened lady asked TripAdvisor if her comment could be taken down.
If this was done, the lawyer's client restaurateur got the desired result - and also deterred others from making similar unfavourable comments.
IMHO, the best way to deal with bad restaurant service, is to 'use your boots to do the talking and walk away, never to return'.
cynic

 - 21 May 2017 15:50
- 76937 of 81564
- 21 May 2017 15:50
- 76937 of 81564
if this lady's comments were indeed malicious rather than based on factual experience, then she was assuredly in the wrong
if her comments were fair and justified, then she should have told the restaurant hotel to sue and be damned
if her comments were fair and justified, then she should have told the restaurant hotel to sue and be damned
ExecLine


 - 21 May 2017 17:29
- 76938 of 81564
- 21 May 2017 17:29
- 76938 of 81564
We will never know.
Moving on.......
Have a look at this and imagine the subject little girl was your little girl
Moving on.......
Have a look at this and imagine the subject little girl was your little girl
MaxK - 21 May 2017 17:45 - 76939 of 81564
Hat tip to mro across the road.
Pay attention. The tories have just committed electoral suicide:
Stealth tax
In fact, even the Bow Group, itself a Conservative think tank, has called the proposals the “biggest stealth tax in history”:
"It is a tax on death and on inheritance. It will mean that in the end, the government will have taken the lions share of a lifetime earnings in taxes. If enacted, it is likely to represent the biggest stealth tax in history and when people understand that they will be leaving most of their estate to the government, rather than their families, the Conservative Party will experience a dramatic loss of support."
Full article here: https://www.thecanary.co/2017/05/21/damian-greens-car-crash-interview-marr-reveals-true-cost-tory-manifesto-pensioners/
Pay attention. The tories have just committed electoral suicide:
Stealth tax
In fact, even the Bow Group, itself a Conservative think tank, has called the proposals the “biggest stealth tax in history”:
"It is a tax on death and on inheritance. It will mean that in the end, the government will have taken the lions share of a lifetime earnings in taxes. If enacted, it is likely to represent the biggest stealth tax in history and when people understand that they will be leaving most of their estate to the government, rather than their families, the Conservative Party will experience a dramatic loss of support."
Full article here: https://www.thecanary.co/2017/05/21/damian-greens-car-crash-interview-marr-reveals-true-cost-tory-manifesto-pensioners/
Fred1new

 - 21 May 2017 17:58
- 76940 of 81564
- 21 May 2017 17:58
- 76940 of 81564
Theresa has started to work out the true probable cost of Brexit and scrambling for ways to pay for it.
She and her motley crew are beginning to be seen as"lying" to the voters hoping to hang on to power.
She and her motley crew are beginning to be seen as"lying" to the voters hoping to hang on to power.


